Emerging Technology
- Post By: Greg Crumpton
- Date:
- Category: Blog
- Tags: AirTight Facilitech, commitment, Excellence, GregCrumpton
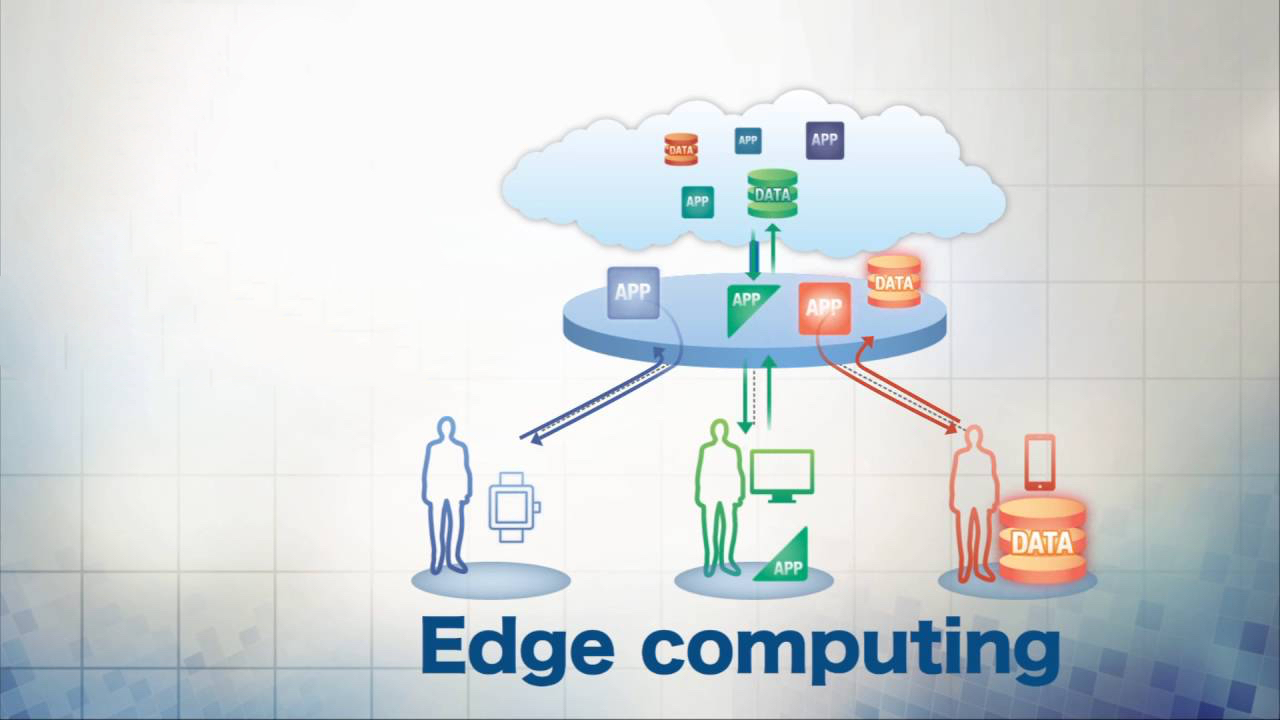
You have undoubtedly heard the Term, “Edge Computing”. Well, what does that mean and why should you care? Consider the amount of data being gathered by Big Box stores, by machines as they talk to one another, by traffic signals, etc. There is just a tremendous amount of data that simply does not need to go all the back to the “central server” or the massive “cloud”, it is fine to remain either on-site and/or very close in proximity to where the data is being harvested and being used.
As stated by Schneider Electrics Steve Carlini in his White Paper #226: “Internet use is trending towards bandwidth-intensive content and an increasing number of attached “things”. At the same time, mobile telecom networks and data networks are converging into a cloud computing architecture. To support needs today and tomorrow, computing power and storage is being inserted out on the network edge in order to lower data transport time and increase availability. Edge computing brings bandwidth-intensive content and latency-sensitive applications closer to the user or data source”.
Consider there are three types of edge computing. Local devices, a localized data center and a regional small or medium data center. All of these will mean and be brought to life by different folks needing to do different things with their data. One of the advantages with the edge concept is less latency in data transmission. Meaning, data, being voice, pure numbers, video or whatever you are transporting on the network can be done quicker without buffering or delays.
In a short summary, edge computing is simply letting data live and function near or at where it is created and needed. As declared by Wikipedia, the advantages are:
1. Edge application services significantly decrease the data volume that must be moved, the consequent traffic, and the distance the data must go, thereby reducing transmission costs, shrinking latency, and improving quality of service (QoS).
2. Edge computing eliminates, or at least de-emphasizes, the core computing environment, limiting or removing a major bottleneck and a potential point of failure.
3. Security is also improved as encrypted data moves further in, toward the network core. As it approaches the enterprise, the data is checked as it passes through protected firewalls and other security points, where viruses, compromised data, and active hackers can be caught early on.
4. Finally, the ability to “virtualize” (i.e., logically group CPU capabilities on an as-needed, real-time basis) extends scalability. The edge computing market is generally based on a “charge for network services” model, and it could be argued that typical customers for edge services are organizations desiring linear scale of business application performance to the growth of, e.g., a subscriber base.
Edge is here to stay, yes it will ebb and flow as Moore’s Law continues to roll and for that matter, gain speed, I am a nay-sayer to Moore’s Law being dead, but none-the-less, it is a fixture to know about and to understand how it will and does currently impact us all.
Leave a Reply
You must be logged in to post a comment.